IT Security Audit Services UAE 2026 — Internal, Compliance & VAPT Audits
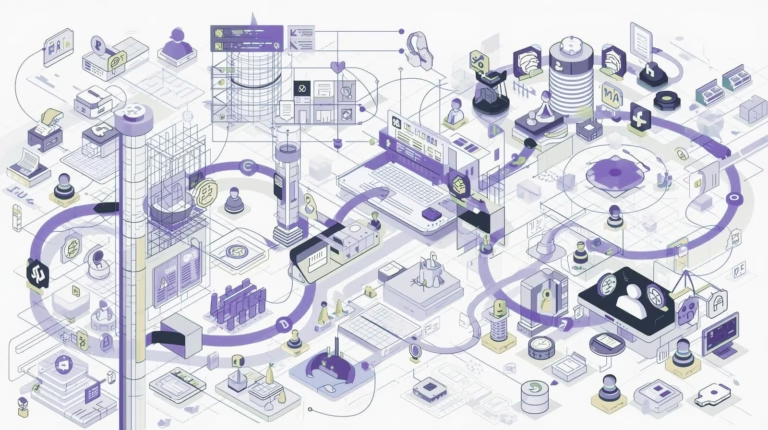
Every year, UAE regulators — the Central Bank, NESA, and the UAE Cybersecurity Council — require organisations to demonstrate that their security controls actually work. A written policy is not enough. An IT security audit provides the independent evidence that…







