In this article we will be diving deep about this interesting topic Top EDR Solutions.

Now, let us see what it means !
EDR Tools
EDR tools are technology platforms that can notify security teams of malicious activities and allow for quick analysis and containment of endpoint threats. An employee workstation or laptop, a server, a cloud system, or a mobile or IoT device can all be considered endpoints.
EDR systems typically collect data from endpoints, such as process execution, endpoint communication, and user logins; analyze data to spot anomalies and malicious activity; and log data about harmful activity, allowing security teams to investigate and respond to issues. They also allow automated and human actions to be taken to control threats on the endpoint, such as isolating it from the network or wiping and reimaging it.
Let us view its security capabilities.
Security Capabilities
Integration
By collecting and aggregating data, EDR solutions provide greater visibility into endpoints. Because endpoint security cannot protect against all threats, it should be combined with other security measures. Organizations should make sure that the EDR product they select integrates seamlessly with their current stack.
Forensic
EDR tools provide forensics capabilities to aid in the tracking of threats and the detection of similar activities that might otherwise go unnoticed. It can assist in establishing timelines and identifying affected systems prior to a breach.
Automate
Advanced EDR solutions can remedy activities automatically. Stop or disconnect infected processes and notify relevant parties, for example, and isolate or disable suspected endpoints and accounts.
Response
Response elements in EDR products assist operators in resolving and investigating issues. Advanced tools can also aid in the investigation of live system memory, the collection of artefacts from suspected endpoints, and the combination of historical and present situational data to construct a holistic picture during an incident.
Insight
Only data gathering and aggregation are provided by basic EDR tools. Analysts can use the tool to look at aggregated data, spot trends, and draw insights manually. Artificial intelligence (AI) techniques and machine learning are used in advanced EDR solutions to automate threat detection and alerting processes. By mapping suspicious behavior to the MITRE ATT&CK architecture, some technologies can spot trends.
Functioning Of EDR
Ingesting from end points
By installing software agents on each endpoint through other, indirect techniques, the system collects telemetry data from endpoints.
Forwarding telemetry to EDR platform
Data from all endpoint agents is sent to a central location, which is commonly a cloud-based EDR platform. To meet regulatory needs, it can also be used on-premises or in a hybrid cloud environment.
Analyzing Data
Machine learning is used to correlate and evaluate the data in this solution. This technique is typically used to build a baseline of normal endpoint operations and user behaviour before looking for anomalies.
Threat intelligence feeds are included in certain EDR platforms to provide context in the form of real-world examples of cyberattacks. To detect attacks, the system compares network and endpoint activity to these samples.
Responding to suspicious activity
The technology detects suspicious activities and sends out alerts to security analysts and other appropriate employees. It also sends out automated messages in response to pre-set triggers. For instance, isolating an endpoint momentarily to prevent malware from spreading across the network.
Retaining Data
Data from EDR solutions is saved for future investigations and proactive threat hunting. This data can be used by analysts and tools to combine incidents into a single incident and examine ongoing or previously unknown attacks. It can also help security experts and tools actively look for harmful activity by providing context for threat hunting.
Top EDR Solutions
Cynet

– The 360 Security Platform is a comprehensive security system that offers NGAV, EDR, UEBA, deception, network monitoring, and protection in addition to endpoint protection.
– Features of EDR :
– Utilizing the integrated security platform, correlation offers visibility into user and network activities as well as endpoint-specific behavior.
– Validation—the correlation of all activity signals allows for stringent validation of any questionable behavior, which lowers the likelihood of false positives.
– Alert: On a single screen, it delivers all the information necessary for quick and effective triage, prioritization, and next steps.
– Deep investigation—immediate access to data from all endpoints, with granular search criteria to view all associated malicious activity that is relevant to the local discovered incident.
– Control is possible at the host, file, and process levels with remediation, ranging from complete host isolation to invasive procedures like scheduled job elimination.
– When a comparable incident recurs, automation makes it possible for customized remediation workflows to be executed automatically.
– Threat hunting—by offering validated IOC repair actions, analysis is able to search for risks throughout the environment and find concealed attack instances.
RSA NetWitness EndPoint
A product with an emphasis on EDR features is RSA NetWitness Endpoint. As part of the larger NetWitness Platform, malware protection, network monitoring, log analysis, and other features are provided.
– Features of EDR
– Access to processes, executables, events, and user behavior through ongoing endpoint monitoring
– Rapid Data Collection—uses a lightweight agent to quickly produce endpoint inventories and profiles.
– Scalable and effective, storing data in a central database and scaling easily to hundreds of thousands of endpoints.
– Baselining “typical” endpoint behavior, spotting deviations, and prioritizing incidents based on possible danger level are all aspects of behavioral detection with UEBA.
– Analyses the cause of the attack and its entire breadth.
CrowdStrike Falcon
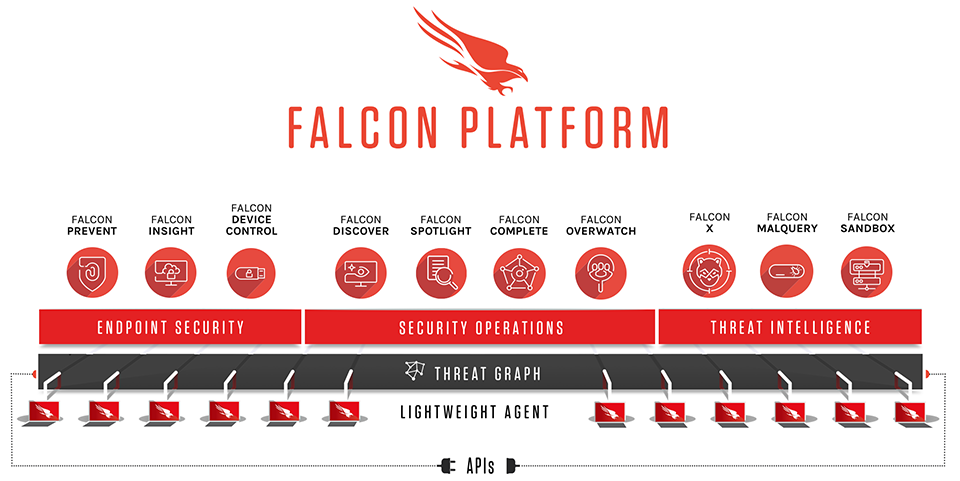
- Detects covert attackers automatically by using behavioral analytics to identify suspicious activities.
- Leverages threat intelligence to accelerate detection of malicious behaviors, tactics, techniques, and procedures.
- Provides real-time and historical visibility into hundreds of security-related events, including process creation, driver loading, registry changes, disk access, memory access, and network activity.
- Quickly isolates endpoints under attack from the network while offering built-in remote execution commands for running scripts, deleting files, and restarting or shutting down devices.
- Empowers analysts to explore the file system, view active processes, access Windows event logs, extract process memory, and collect environment variables using information collectors.
- Enables teams to respond swiftly and decisively to contain or remediate threats with actionable remediation capabilities.
FireEye End Point Security

– An agent with four detection engines, NGAV capabilities, and EDR are all included in this endpoint solution.
– Features of EDR :
– Analysis of threat indicators is made possible by Triage Viewer and Audit Viewer.
– Helps analysts identify and contain risks using enterprise security search
– Comprehensive endpoint inspection and analysis of data acquisition
– Endpoint exploit processes are detected and alerted by Exploit Guard.
Cybereason End Point Security

– A component of the Cybereason Defense Platform, along with Managed Detection and Response and NGAV (MDR).
– Features of EDR :
– Threat analysis—displays the full process tree, the timing, and each process’s share of malicious behavior across all machines.
– Third-party alerts—comprised of firewall and SIEM tool alerts as well as EDR data alerts
– Attack complete scope: View all associated attack components, such as the attack’s root cause, the computers and people it affected, any affected communications, and the attack’s timing.
– Customization, including behavioral allowlisting and custom rules.
– Execute commands from a full toolbox for guided remediation on the endpoint to gain access to a remote shell.
– Enterprise-wide remediation—responds to threats affecting a large number of machines by carrying out remediation procedures simultaneously on all impacted devices.
SentinelOne

– SentinelOne incorporates static artificial intelligence (AI) to deliver real-time endpoint protection and lessen false positives that sabotage investigations or make threat identification a costly procedure.
– Features of EDR :
– Detecting threats
– Threat assessment
– Prevention Assisted by AI
– Automatic Reaction
– Platform Singularity from SentinelOne
– Ranger Sentinel One
Conclusion
That’s all about the Top EDR Solutions. After reading this essay, I hope you found it enjoyable and learned something new. We have learned what are EDR Tools, its security capabilities, functioning of EDR, and EDR solutions which are used in real-time.
Protect Your Business with Enterprise-Grade Cybersecurity
eShield IT Services provides VAPT, managed SOC, ISO 27001, PCI DSS & incident response for UAE, Saudi Arabia & India. CISSP & OSCP certified team. Free risk assessment.
Get a Free Security Assessment →

